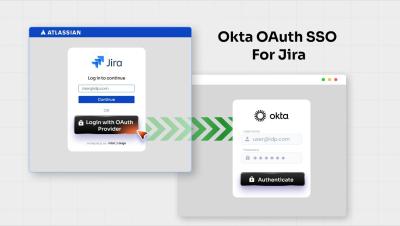
How to Configure Jira OAuth/OIDC SSO Integration with Okta | Step-by-Step Guide
Manually managing user authentication in Jira can lead to security gaps and administrative overhead. By integrating Okta with Jira using the miniOrange OAuth/OIDC SSO plugin, you can provide your team with a seamless, secure, and centralized login experience. In this video, we walk you through the entire end-to-end configuration: from setting up a Web Application in the Okta Admin Console to finalizing the OAuth settings within Jira. You’ll see exactly how to map Client IDs, secrets, and endpoints to get your SSO up and running in minutes.