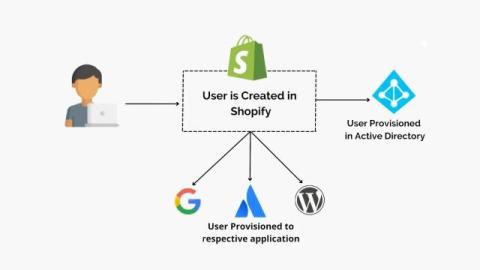
What Is SCIM Provisioning and How It Works in Shopify
SCIM provisioning, or System for Cross-Domain Identity Management provisioning, is a standardized way to automate the process of creating, updating, and removing user accounts across multiple applications. Instead of manually adding or deleting users in each platform, SCIM provisioning ensures that any change made in one system is instantly reflected in all connected systems. This keeps user data consistent, reduces admin workload, and improves security.