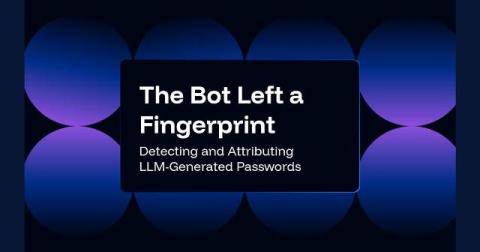
Are we blindly giving AI access to everything?
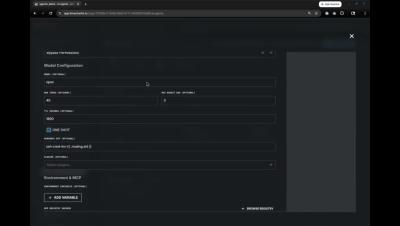
Users are connecting AI tools without understanding the security implications. In this week's Intel Chat, Chris Luft and Matt Bromiley discuss a security breach at Vercel that originated from a compromised third-party AI tool used by one of its employees. The attacker gained control of the employee's Google Workspace account, which provided access to Vercel's internal environment.