Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
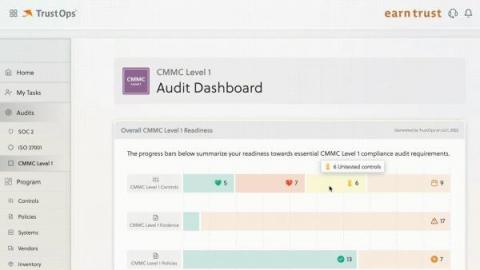
Kintent Trust Cloud Supports CMMC Level 1
Achieving CMMC compliance is no easy feat. CMMC requirements are stricter than most, and focus heavily on documentation. This certification is also still relatively new, so it’s constantly undergoing changes.
Clearing the air over the new CERT-In rules
Authorities that lay down compliance regulations often update them in order to keep them relevant. However, for organizations that fall under the purview of these regulations, it can be a challenge to keep up with the updates and ensure that they stay compliant.
Why Security Configuration Management (SCM) Matters
In the Godfather Part II, Michael Corleone says, “There are many things my father taught me here in this room. He taught me: keep your friends close, but your enemies closer.” This lesson Vito Corleone taught his son Michael is just as applicable to IT security configuration management (SCM).
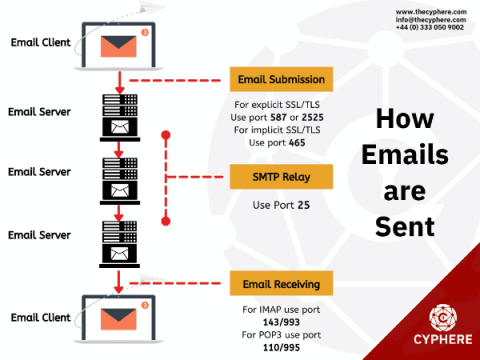
Secure SMTPs Port - Which are Secure SSL Email Ports (25,465,587 & 2525)
When configuring an email client application or an email server to send to relay emails, many questions come to one’s mind, such as which SMTPs should be used, what is the purpose of each of these ports, which are standard ports, which ports allow secure communication and many more.
The Top 10 SMB cyber security mistakes. Find out how to fix these security risks.
Small and medium businesses are the backbone of many economies, yet they often do not have the same level of cybersecurity as larger businesses. This is because they think that they are too small to be a target, or they believe that their cybersecurity measures are adequate. In this blog post, we will discuss why SMBs are doing cyber security wrong – and how to get it right!
Key cybersecurity measures for the fashion industry
Cyberattacks often target the retail sector, although many of these threats are aimed at the e-commerce channel, businesses have also reported incidents where in-store Wi-Fi access points and even IoT devices are exploited as attack vectors. This is reflected in several studies, which reveal that, together with the education sector, the fashion industry was one of the hardest hit last year and 60% of retail companies are at risk of suffering an attack.
OWASP Top Ten: Injection
Injection is one of the top OWASP vulnerabilities for a reason. It can allow attackers to inject their own malicious code into programs, which can result in serious security breaches. This blog post will discuss what injection is, how it occurs, and some of the most common attack vectors. We will also provide tips on how to protect your website and Web Applications from these attacks.
Jason Barnes: How to use automation to remove tedious tasks, mitigate risk, and prioritize the adoption of new capabilities
On today’s episode of the Future of Security Operations Podcast, Thomas speaks with Jason Barnes — the former Head of Global Security Operations at Netskope and current Senior Director at Charter Communications.
June Developer Roll Up
The team at LimaCharlie continues on its mission to develop the concept of Security Infrastructure as a Service. We added three new team members during the month of June with more coming! We also hosted a webinar on securing your CI/CD pipeline built around some new capabilities we added which allow for the ingestion and monitoring of GitHub audit logs. You can watch a recording of that webinar here: SecDevOps & LimaCharlie - Automating and auditing of GitHub access