Launching Your Penetration Testing Career
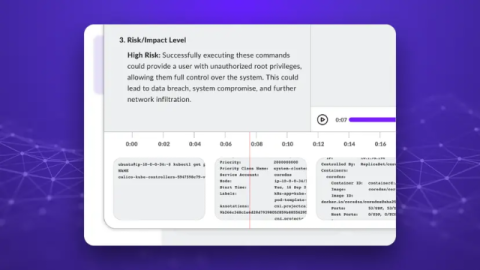
Penetration testing is often seen as one of the most exciting jobs in cyber security. After all, who wouldn’t want to be the person trusted to break into systems before the criminals do? It’s a career that’s in high demand, with competitive salaries and no shortage of opportunities, but getting into pentesting isn’t always straightforward.