Webinar Recap: Using Technology To Enhance Multifamily Experiences
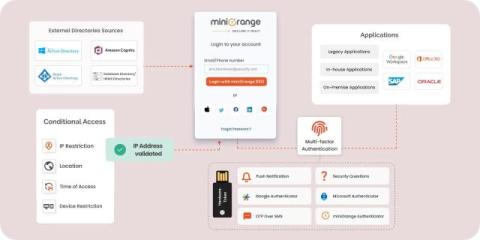
The tools and technologies used to secure living spaces are constantly evolving, as are residents’ expectations for more convenient features and amenities. This raises an important question for property managers: how can they meet residents’ expectations while providing the enhanced security they need?