Continuous Vendor Risk Monitoring: Real-Time Cyber Risk Visibility with Bitsight
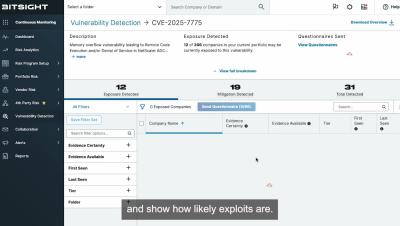
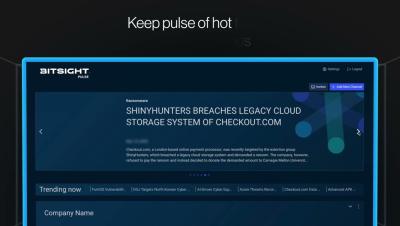
Gain real-time visibility into cyber risks across your entire vendor ecosystem with Bitsight Continuous Monitoring. Continuously track third- and fourth-party security performance, uncover hidden vulnerabilities, and identify high-risk changes before they impact your business. Powered by the industry’s most comprehensive cyber risk data, Bitsight helps security and GRC teams respond faster to critical threats—including zero-day vulnerabilities—while improving vendor collaboration and strengthening overall supply chain resilience.