Trust in the age of AI for fintech auditors
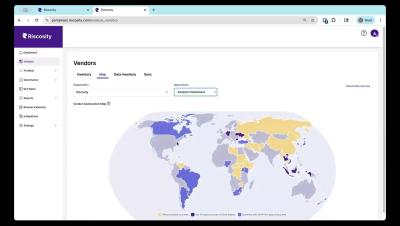
There is an old saying: Trust, but verify. For Third-Party Risk Management auditors in regulated financial institutions, that principle has never been more relevant. Vendor questionnaires, SOC 2 reports, and annual reassessments are no longer enough. Regulators are moving beyond paper-based oversight and toward operational proof. The new expectation is clear: Show where customer data is actually flowing. Prove that you control it.