SASE Instant High Availability and Why You Should Care
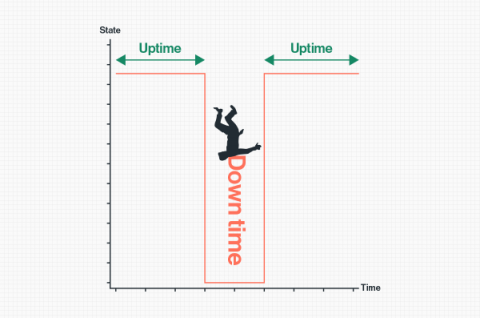
High availability may be top of mind for your organization, and if not, it really should be. The cost range of an unplanned outage ranges from $140,000 to $540,000 per hour. Obviously, this varies greatly between organizations based on a variety of factors specific to your business and environment. You can read more on how to calculate the cost of an outage to your business here: Gartner.