Malicious Code Deletes Directories If You Do Not Have a License
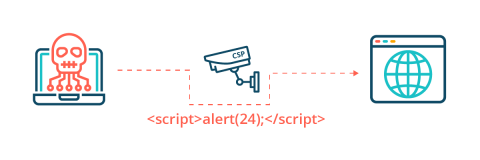
Our research team here at Mend has identified a new kind of malicious code that attackers can use to exploit genuine concerns about security and licenses. The code in the case below is used to prevent people from using unlicensed software, specifically by removing the code if it detects that the software is not licensed during the deployment stage. The code is tricky to understand and uses a web request to check if the software is being used legally.