Top 5 Proactive Threat Intelligence Use Cases for Enhanced Cyber Defense
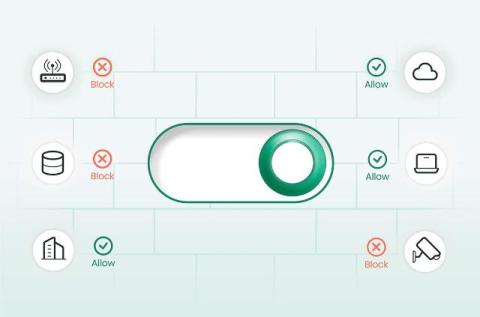
In this fast-moving world where businesses operate completely through IT infrastructure, waiting for a threat to happen and finding a solution isn’t enough. There should be a proactive approach, where you spot and remove a threat even before it touches your systems.