Mythos, MOAK, CTEM and the End of CVE Chasing
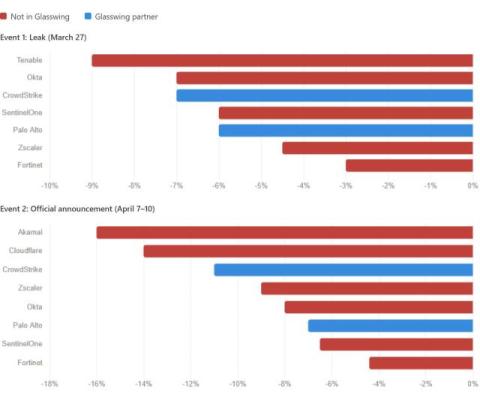
A few weeks ago the world was exposed to Mythos, Anthropic's new frontier model and the Project Glasswing announcement that came with it. The reaction across the industry was immediate. Cybersecurity stocks fell sharply. The Treasury Secretary convened an emergency meeting with major bank CEOs. 250 CISOs produced a response playbook over a single weekend. That is not a typical announcement or a PR "leak". That is a reckoning. Then, about a week later, I came across MOAK.