8220 Gang Continues to Evolve With Each New Campaign
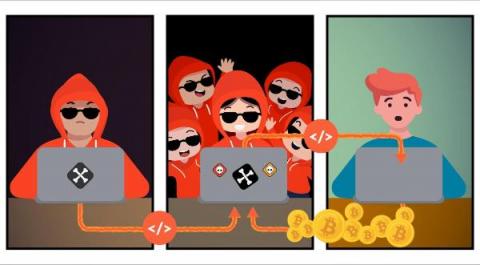
8220 Gang has been dubbed as a group of low-level script kiddies with an equally disappointing name based on their original use of port 8220 for Command and Control (C2) network communications dating back to 2017. Since an initial Talos report in late 2018, the group has continued to use, learn, and benefit from the efforts of their counterparts in the cryptojacking world.