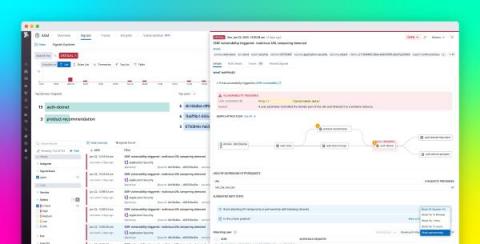
Microsoft Power Platform DLP Bypass Uncovered- Finding #2 - HTTP calls
Low-code and no-code technologies are being embraced across the world, but there’s one LCNC platform that stands out, with significant growth and enterprise adoption – and that’s Microsoft’s Power Platform.