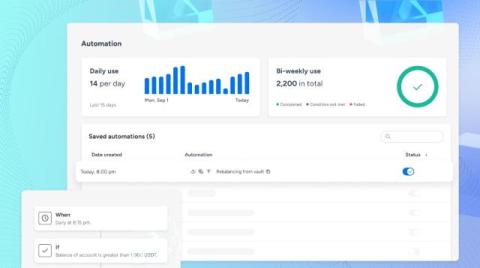
1Password partners with TD SYNNEX to make Extended Access Management available for IT service providers
At 1Password, our mission has always been clear: to provide robust, human-centric security solutions that meet the needs of today’s businesses. Cybersecurity threats are evolving daily so it’s never been more important for businesses to have reliable, user-friendly solutions.