Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Security
Trustwave Recognized in Gartner's 2022 Market Guide for Managed Security Services
Gartner has recognized Trustwave as a Representative Vendor in the analyst firm’s March 2022 Market Guide for Managed Security Services (MSS). In addition, Gartner previously recognized Trustwave as a leader in its MSS solution in its 2019 Gartner “Magic Quadrant for Managed Security Services, Worldwide.”
What is Policy Based Access Management?
We’re excited to be included in the first Policy Based Access Management (PBAM) market report! The KuppingerCole Analysts AG’s 2022 Market Compass provides an excellent overview of how the access market is transforming and emerging vendors in the space.
How to generate a Software Bill of Materials (SBOM) using Veracode Software Composition Analysis
Generating fake security data with Python and faker-security
Snyk recently open sourced our faker-security Python package to help anyone working with security data. In this blog post, we’ll briefly go over what this Python package is and how to use it. But first, we’ll get some context for how the factory_boy Python package can be used in combination with faker-security to improve your test-writing experience during development. Note: Some knowledge of Python is helpful for getting the most out of this post.
"Pipedream" Malware Targets ICS: What Critical Infrastructure Owners Need to Know
Troubling new malware designed to facilitate attacks on a wide array of critical infrastructure – from oil refineries and power plans, to water utilities and factories – is raising concerns for its versatility. The malware, named Pipedream by Dragos and Incontroller by Mandiant, who have both tracked and researched the toolkit, is potentially capable of gaining full system access to multiple industrial control systems (ICS) and supervisory control and data acquisition (SCADA) devices.
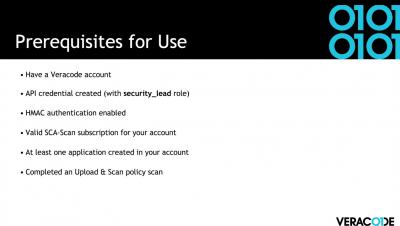
How to Generate an SBOM in Veracode SCA
Emerging government regulations have driven the advancement of standards for securing software supply chains. The production of a Software Bill of Materials (SBOM) in a standard format is an increasing audit and compliance need for large organizations.
Improve your patching efficiency with Tripwire State Analyzer
Organizations are always concerned with improving efficiencies to make business flow smoother. Some of the biggest inefficiencies in any business revolve around time wasted on operational tasks. Whether it is a stale accounting process, or something as trivial as routing phone calls to the proper department, saving time by improving a process can mean more profits, which is what business is all about.
How OAuth 2.0 Works
The modern human likely has profiles on dozens of applications. Whether it’s social media applications, music/video streaming, or workspace resources, each of us must manage accounts that contain personal information. Over time, these siloed applications have become increasingly connected. Twitter allows news sites to directly tweet, Discord searches Facebook for suggested friends, and Jira creates user accounts using Github profiles.