Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Security
3 Ways Using ASVS Can Help Your Organization
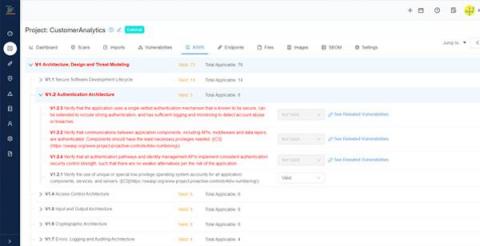
As digital transformation continues to take over the world, security increasingly becomes a concern for companies of all sizes. No matter how big of a security team you might have, it is hard to speak a common language between security and development teams on what controls you need during the software development life cycle. To tackle this problem, OWASP has released Application Security Verification Standard towards the end of 2021.
SLA Levels on Kondukto
Understanding SAML SSO, the basics from the user side
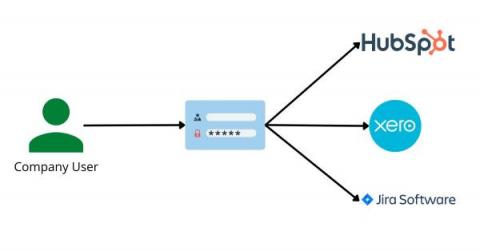
I have always worked in tech, so have always needed to understand the technical nature of the products we are building. This process has always been over-complicated for me so I now always try to write a guide for non-technical people like me. It turns out that once you understand it you can explain it to other non-technical people much easier! So here we go as I try to explain SAML (Security Assertion Markup Language) SSO (single sign-on) and why BoxyHQ makes it so easy to implement.
Understanding SAML SSO, the basics from the solution provider's side
This article follows my first article in which I explain the basics of SAML from the users' side. If you haven't read that one already I would recommend reading that one first here. In this article, we are going to take a look at what SAML authentication and setup look like from the solution providers' perspective. If you are a B2B solutions provider and you plan to have enterprise customers they will likely ask that your product supports SAML SSO.
Kubernetes API Access Security Hardening.
In a Kubernetes cluster, Control Plane controls Nodes, Nodes control Pods, Pods control containers, and containers control applications. But what controls the Control Plane? Kubernetes exposes APIs that let you configure the entire Kubernetes cluster management lifecycle. Thus, securing access to the Kubernetes API is one of the most security-sensitive aspects to consider when considering Kubernetes security.
Your Ultimate Social Media Security Checklist [2022 Updated]
Social media is both a boon and a bane. While it has connected billions of people, made them more accessible, and created more possibilities for the end-users. There's no doubt that it has also made them more susceptible to security threats and vulnerabilities. According to We Are Social, there are around 4.62 billion active social media users worldwide. This is precisely the very reason why cyber criminals love social media as well.
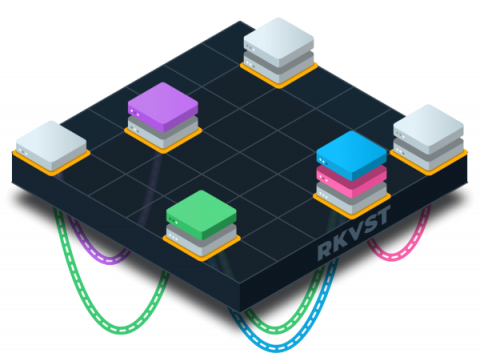
Understanding and Preventing Configuration Drift
Proper management of the configuration of your infrastructure components is vital to security, compliance and business continuity. Unfortunately, configuration drift in systems and applications is common, which leaves the organization vulnerable to attack. Indeed, about 1 in 8 breaches result from errors such as misconfigured cloud environments, and security misconfiguration ranks #5 on the OWASP list of the top 10 web application security risks.
LockBit Ransomware Gang Introduces the First Ransomware Bug Bounty Program in the Dark Web
Read also: RansomHouse extortion gang allegedly stole 450GB of data from AMD, one of Iran’s major steel companies was hit by a cyberattack, and more.
What is Zero Trust Fabric?
Trust is a very broad and complex topic, and consequently there are very many definitions of Zero Trust that can be confusing as they try to capture the nuance and details and scope that the problem of trust raises.