Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Blog
DDoS attack prevention and protection explained
This blog was written by a third party author. Distributed denial of Service (DDoS) attacks stand as some of the most disruptive and costly cyberattacks that organizations face on a regular basis. Cyber criminals use DDoS attacks to make websites and other online services unavailable for legitimate use.
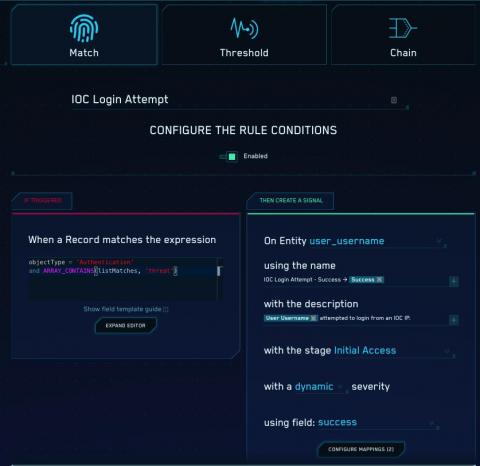
Practical security engineering: Stateful detection
Detection engineering at Elastic is both a set of reliable principles — or methodologies — and a collection of effective tools. In this series, we’ll share some of the foundational concepts that we’ve discovered over time to deliver resilient detection logic. In this blog post, we will share a concept we call stateful detection and explain why it's important for detection.
The damaging impact data breaches have on American society as a whole
This blog was written by an independent guest blogger. In the age of the internet where everyone has a mobile phone and multiple social media profiles, one phrase has become synonymous with doom and dread - data breach. It seems like these breaches have become a regular occurrence in modern society. Small businesses may be particularly susceptible to security hacks, but even large corporations are not immune.
Improve network security with traffic filters on Elastic Cloud
Today we are pleased to announce new traffic management features for Elastic Cloud. Now you can configure IP filtering within your Elastic Cloud deployment on Amazon Web Services (AWS), Google Cloud, and Microsoft Azure. We are also announcing integration with AWS PrivateLink. These features help give you greater control over the network security layer of your Elastic workloads.
Detectify achieves ISO 27001 Certification
STOCKHOLM — July 14th, 2020 — Detectify, the Sweden-born cybersecurity company that offers a website vulnerability scanner powered by Crowdsource – a network of ethical hackers, today announced that it has achieved the internationally recognized standard ISO/IEC 27001:2013 certification.
Supercharged SOAR: Meet Splunk Phantom 4.9
The number of cyberattacks launched on organizations continues to rise every year. More attacks means more security alerts that security analysts have to triage each day. Many security teams have turned to a security orchestration, automation and response (SOAR) tool to help them automate the ever-increasing volume of security alerts, and respond to threats faster and more comprehensively.
Teaching kids skills to catch hackers and fix security risks at Cyber Discover
We are now living in an era where kids are growing up with the internet every day. Those of us who are older learned how to be more skeptical of technology, but our children largely aren’t growing up with this same level of skepticism. Today, over 60% of children are using the internet for over forty hours a week. Many of these children are taking cybersecurity for granted because they simply aren’t aware of many of the digital security risks that come with online use.
Shift Left Security with Golang in VS Code
Most modern software today has moved aggressively into using third-party open source dependencies to reduce duplication and accelerate development by using pre-existing code.
Transform IT With File-sharing Services For the Future
As more and more businesses were forced to move to the cloud with the COVID-19 crisis, content and data have proliferated across devices, users, apps, and locations as a result of the new, mass work-from-anywhere reality. This brought a growing set of challenges to prevent data silos and content sprawl while remaining compliant with data regulations and governance.