Multi-Source Telemetry: Finding Business Email Compromise
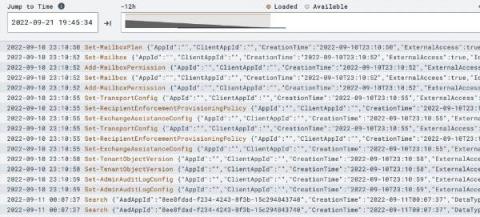
This post is the first of a multi-part blog series on various sources of telemetry. At LimaCharlie, we’re a firm believer in visibility. The more an analyst can see about their environment, the more impactful decisions they can make. We are huge fans of multi-source telemetry, bringing visibility from almost anywhere in your environment to one place for analysis, detection, and response capabilities.