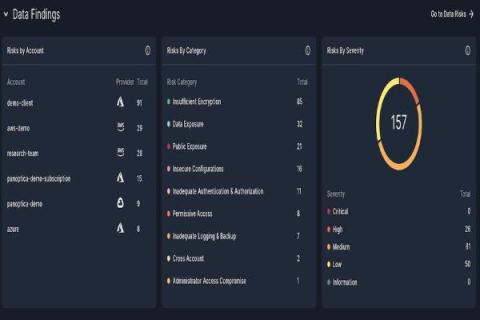
GenAI Attack Path Remediations for Panoptica
Generative AI technology is rapidly evolving, offering groundbreaking capabilities in various fields, including cloud native environments and CNAPP (Cloud-Native Application) solutions. Development of generative AI technology holds immense promise for enhancing the capabilities and performance of cloud-native environments and CNAPP solutions.