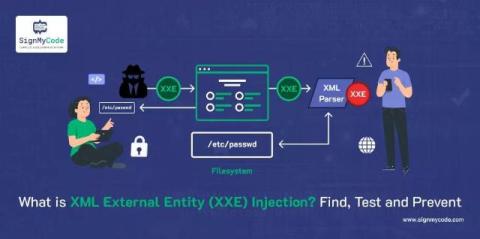
What is XML External Entity Injection? Find, Test and Prevent XXE Vulnerabilities
XML external entity injection or XXE, is a type of web security vulnerability and an application-layer cybersecurity attack. This vulnerability allows the hacker to interfere with an application while it is processing XML data. The attacker can inject unsafe XML entities into the application and can interact with systems to which the application has access. The hackers can also view files on the server and even perform remote code execution (RCE).