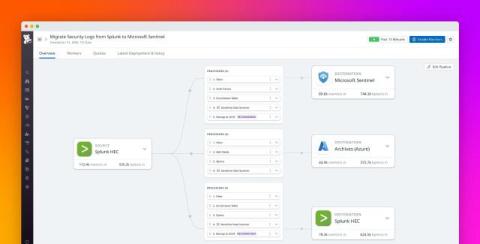
Simplify your SIEM migration to Microsoft Sentinel with Datadog Observability Pipelines
As cyberattacks rise in number and sophistication, many CISOs are pushing their organizations to adopt modern SIEM solutions to better monitor and investigate threats to their applications and infrastructure. Enterprises with a large Microsoft Azure or Windows-based footprint in particular are increasingly eyeing Microsoft Sentinel to consolidate their security stack and workflows.