Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Obrela at Delphi Forum || Panel Discussion
Shine a Light on Shadow IT: Vanta Launches Category-First Vendor Risk Management Solution
World Password Day: Tips, quiz, and tools to improve password security
Password security, though sometimes underrated, is crucial for an organization to remain viable in the vast digital landscape. A popular quote on the internet says, “A good neighbor is someone who does not put a password on their Wi-Fi.” However, for a good company, the opposite holds true, as they must thoroughly secure all their resources.
Password Managers: Here to stay?
Zero Trust Security in Active Directory and Azure AD Groups
One important way of securing your organization against attacks and other cyber threats is to implement a Zero Trust security model for groups (distribution lists, security groups, Microsoft 365 groups) in on-premises Active Directory and Azure AD. After all, these groups control access to your IT assets, from sensitive data to vital communications channels and tools like Microsoft Teams and SharePoint.
How Does a WAF Work?
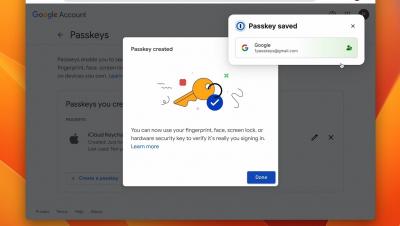
Sneak peek: save and use a passkey to sign in to your Google account
Cybersecurity Risk Mitigation: Understanding the Limitations of Reducing a £2 Million Risk
Zero day remediation tips: Preparing for the next vulnerability
Businesses increasingly run on software, which, unbeknownst to its developers, can contain vulnerabilities that attackers often discover and exploit before a patch is available. This makes zero day attacks inevitable, but you can reduce their impact in your network and across your supply chain if you’re prepared to act fast.