Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
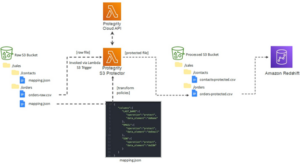
Coast Capital Savings Credit Union: Meeting Canadian Regulatory Standards for Compliance with Protegrity
One of Canada’s largest credit unions, Coast Capital Savings Credit Union (CSS), with over 50 branches across the country, needed to protect critical PII data stored in their AWS cloud environments, Amazon Redshift, AWS EMR, and AWS S3. CSS had to meet Canadian regulatory standards for compliance in 2021, including the Personal Information Electronic Documents Act (PIPEDA), along with a data transformation initiative surrounding its architecture.
How to Protect Customer Data in Zendesk - Part 2: Addressing Sensitive Data Growth
The proliferation of sensitive data continues to grow unabated, particularly for support agents using Zendesk. The Zendesk’s CX Trends 2022 Report found that ticket volume had increased across all channels, with webform/email up 10% YoY and chat up 17% YoY.
Consolidation, Flexibility, ChatGPT, & Other Key Takeaways from Netskopers at RSA Conference 2023
At RSA Conference 2023, a number of Netskopers from across the organization who attended the event in San Francisco shared commentary on the trends, topics, and takeaways from this year’s conference.
Torq Hyperautomation: The Most Talked About Product at RSAC
Don't Manage Third-Party Risk Alone
New research from the Cyentia Institute found that 98% of organizations do business with a third party that has suffered a breach. The report also found that the average firm has 11 third-party relationships and hundreds of indirect fourth- and nth-party relationships. Bottom line: an expanding attack surface makes companies more prone to cyberattacks.
Mastering CMMC Compliance with UTMStack: A Comprehensive and Technical Approach
Achieving and maintaining Cybersecurity Maturity Model Certification (CMMC) compliance is a critical requirement for organizations operating within the defense industrial base. As a comprehensive SIEM solution, UTMStack offers advanced features and capabilities that not only streamline the compliance process but also inspire confidence in security and protection.
LC101: Simplifying enterprise deployment
An overview of the OSI model and its security threats
The Open Systems Interconnection (OSI) model is a conceptual framework developed by the International Standards Organization (ISO). It has been in use for over 40 years, and is cited in every computer network book. It is also a favorite resource for just about every cybersecurity exam. The OSI model is represented in seven layers that help us understand how communications between computer systems occur.
What is Zero Trust? Everything You Need to Know to Secure Vendor Access
Zero trust is a cybersecurity approach that restricts network access so only the right people are accessing the specific information they need —and nothing more. Here’s everything you need to know about the basic principles of Zero Trust and how to apply them to your third-party risk management program (TPRM) to create more secure remote access connections.