Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Next-Level Threat Hunting: Shift Your SIEM from Reactive to Proactive
Using metadata & tstats for Threat Hunting
Using stats, eventstats & streamstats for Threat Hunting...Stat!
Key Threat Hunting Deliverables with PEAK
Amid Sharp Increase in Identity-Based Attacks, CrowdStrike Unveils New Threat Hunting Capability
Adversaries are doubling down on identity-based attacks. According to Nowhere to Hide: CrowdStrike 2023 Threat Hunting Report, we’ve seen an alarming 583% year-over-year increase in Kerberoasting attacks — a form of identity-based threat — and a 147% increase in access broker advertisements on the dark web. Adversaries are evolving their tradecraft, building custom tooling and leveraging more than usernames and passwords to breach your environments.
Threat hunting with Sumo Logic: The Command Line
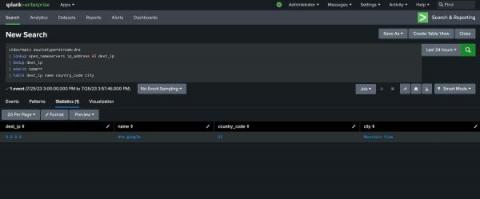
Using Splunk Stream for Hunting: Finding Islands in the Stream (of Data)
Using the Lookup Command for Threat Hunting (Lookup Before You Go-Go)
Using Threat Hunting to Uncover Cybersecurity Threats
In the fast-evolving digital landscape, the prevalence of cyber threats has become a stark reality for businesses and individuals alike. The conventional cybersecurity measures, while essential, are often reactive and inadequate against sophisticated attacks. This is where Threat Hunting emerges as a proactive and dynamic approach to cybersecurity. In this blog, we delve into the fascinating world of Threat Hunting and explore its significance in safeguarding against cyber adversaries.