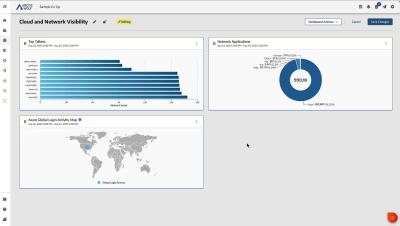
How Arctic Wolf's Custom Dashboards Enhance Visibility
In this demo, explore how the Arctic Wolf unified portal provides visibility into your aggregated security data while also providing flexible visualizations and reporting through custom dashboards.