The MITRE ATT&CK Framework: Command and Control
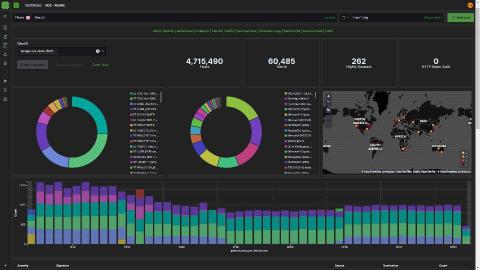
Most malware these days has some level of Command and Control. This can be to exfiltrate data, tell the malware what instructions to execute next, or download encryption keys in the case of ransomware. In each case of command and control, the attacker is accessing the network from a remote location. Having insight into what is happening on the network is going to be crucial in addressing these techniques.