How to Hide Products on Shopify
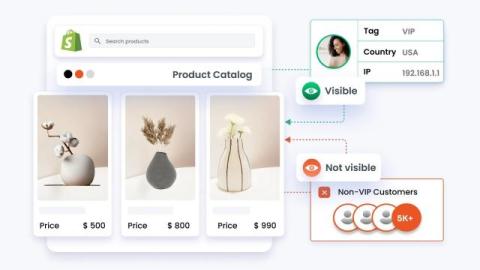
Hiding products on Shopify without deleting them is a common requirement when managing storefront visibility. By default, Shopify doesn’t provide a dedicated “hide product” button, but it does offer various visibility controls using product status, sales channels, and newer features like unlisted products.