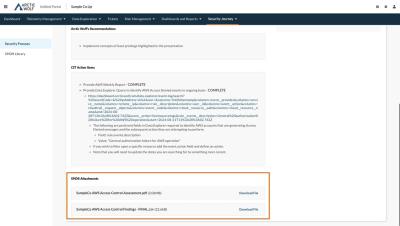
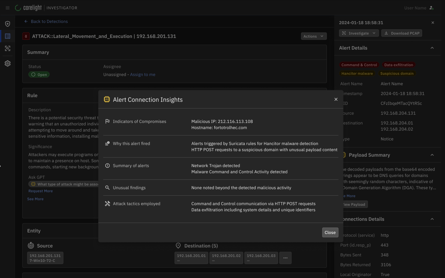
How to Access and Action Arctic Wolf Threat Intelligence
This video demonstrates how Arctic Wolf Threat Intelligence enables customers to defend against new and emerging threats through engaging content, actionable intelligence, and IoC quicklinks.