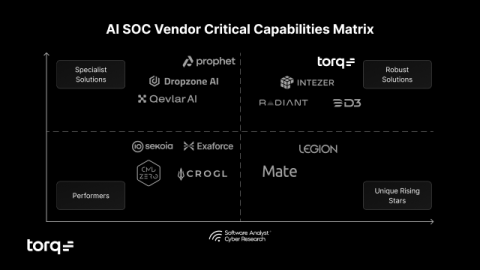
AI SOC Market Landscape 2025: Torq Leads With Hyperautomation
The SACR 2025 AI SOC Market Landscape Report just dropped, and Torq was named one of the “most feature-rich platforms” on the market. Not because we bolted a chatbot onto triage. But because we’ve built an AI SOC platform modern security teams actually need: an AI-native, execution-first infrastructure that operationalizes intelligence at scale. And that platform works.