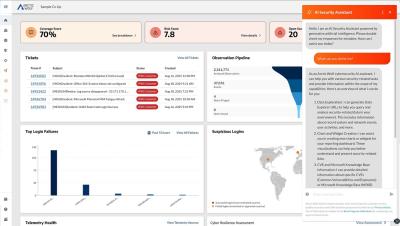
How Arctic Wolf Managed Risk Helps Your Organization Manage the Attack Surface
With Arctic Wolf Managed Risk, organizations can monitor their risk score, discover and assess risks in the environment, report on assets and prioritize remediation activities to the entire security environment. Learn how Arctic Wolf Managed Risk empowers you to discover, assess, and harden your environment against digital risks by contextualizing the attack surface coverage across your networks, endpoints, and cloud environments.