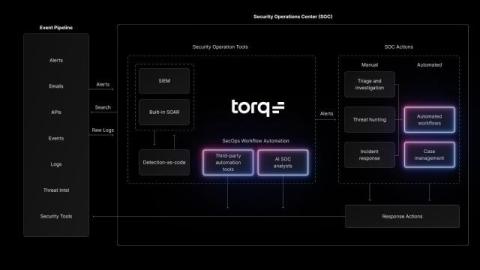
Fidelis Elevate Deep Visibility: The Force Multiplier for Modern Security Operations
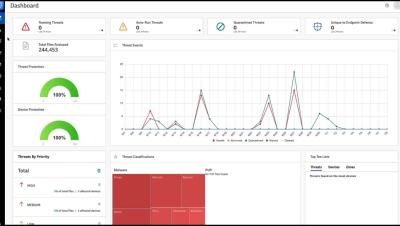
Security teams struggle to detect and respond to attacks across expanding environments. Cloud systems, digital initiatives, and IoT devices have created complexities where standard security fails. Meanwhile, attackers remain hidden while security staff drown in alerts without adequate visibility.