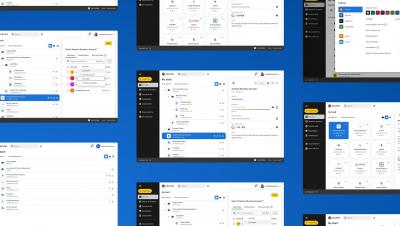
Introducing Keeper's UI Refresh
The Keeper you know and love is getting a fresh, updated look, with a friendlier, accessible and more intuitive experience. Keeper’s new user interface offers clearer distinctions between elements as well as enhanced clarity and navigation – all improving usability in order for our users to take full advantage of Keeper’s powerful features.