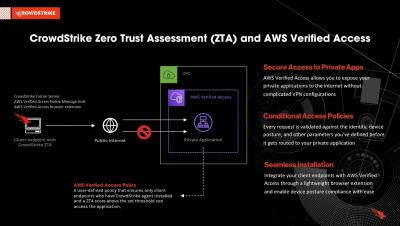
Securing private applications with CrowdStrike Zero Trust Assessment and AWS Verified Access
CrowdStrike Zero Trust Assessment (CrowdStrike ZTA) provides customers the ability to assess their endpoint security posture, allowing AWS Verified Access to provide conditional access to resources that comply with their organization’s device posture policies.