Getting Value from Your Proxy Logs with CrowdStrike Falcon LogScale
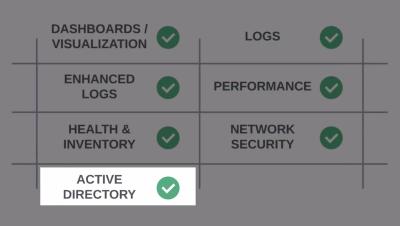
CrowdStrike Falcon LogScale allows you to bring in logs from all of your infrastructure. In this demo watch how quickly you can get value from your Proxy Logs with CrowdStrike Falcon LogScale.