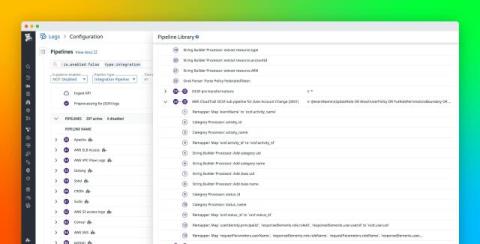
Normalize your data with the OCSF Common Data Model in Datadog Cloud SIEM
Security teams rely on SIEMs to aggregate and analyze data from a wide range of sources, including cloud environments, identity providers, endpoint protection platforms, network appliances, SaaS apps, and more. But every source delivers logs in its own format, with different field names, structures, and semantics. This fragmentation makes it difficult to build scalable, reusable detection rules or correlate threats across systems.