Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
4 opportunities MSPs can leverage from cyber insurance
The rapid escalation of cyberattacks around the world has increased the number of prerequisites to qualify for a cyber insurance policy. If a business faces a cyberattack involving a data breach, it may find it hard to recover without additional support or resources. And this is just one example.
Cyphercon 6
Nearly 1500 cybersecurity professionals gathered in Milwaukee for Cpyphercon 6. Read the highlights from the largest hacker event in Wisconson
GitGuardian Secrets Detectors Q1 2023 Wrap-Up
GitGuardian's Q1 wrap-up highlights our progress in detecting secrets, introducing new secret detectors, and committing to code security. With six new detectors released in Q1, GitGuardian remains the go-to solution for developers looking to write more secure code.
What are Code Signing Certificates and Provisioning Profiles?
A Code Signing certificate is a form of online certificate presented to an organization that is entirely dedicated to software development to validate authenticity and integrity of the programs they create. This type of digital certificate holds significant information and is issued by a CA. Here, a public key is used to bind the organization’s identity. A software developer leverages the power of a Code Signing certificate to sign the executables and applications prior to their release.
Why You Should Scan Your Applications in the Repository
If your application development environment is like most, you’re using more code and you’ve accelerated the development of applications and software. That’s great for productivity, but it presents a big challenge for security, as your developers come under increasing pressure to ship code quickly — while also ensuring that their code is secure. They need to find a sweet spot between speed and security, and scanning at the repository level is the way to go. Here’s why.
CrowdStrike Brings Extended Detection and Response to New z16 and LinuxONE 4 Single Frame and Rack Mount Models
We are excited to collaborate with IBM, which today unveils its new IBM z16 and LinuxONE Rockhopper 4 single frame and rack mount models, available globally on May 17, 2023. Powered by IBM’s Telum processor, these new configurations are designed for highly efficient data centers with sustainability in mind. CrowdStrike customers can make more effective use of their data center space while remaining resilient in the midst of ongoing global uncertainty.
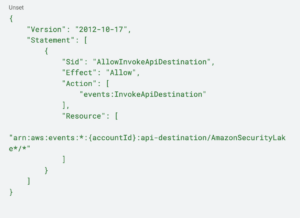
IAM Legend: How Torq is Reinventing Identity and Access Management
Building Efficient SecOps Pipelines with AWS Security Lake and Torq
Italy Bans ChatGPT: A Portent of the Future, Balancing the Pros and Cons
In a groundbreaking move, Italy has imposed a ban on the widely popular AI tool ChatGPT. This decision comes in the wake of concerns over possible misinformation, biases and the ethical challenges AI-powered technology presents. The ban has sparked a global conversation, with many speculating whether other countries will follow suit.