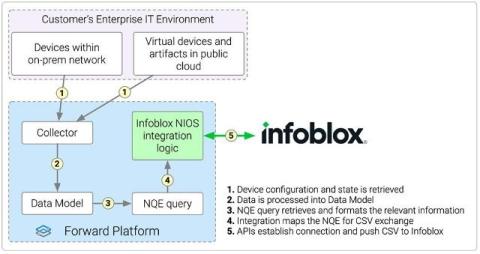
Validated Integration with Infoblox Enhances IPAM Precision and Improves Network Assurance
In today’s hybrid, multi-cloud environments, managing accurate network data and enforcing policy consistency across diverse infrastructures has become a serious operational challenge. As enterprises navigate the complexity of multi-vendor architectures and evolving security requirements, gaps in IPAM (IP Address Management) accuracy can lead to operational disruption, misconfigurations, and audit risk.