Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Remote Work and Data Security: The Human Factor
If you read our earlier blog, you know Egnyte commissioned a study to better understand how COVID-19 has impacted businesses’ ability to maintain data security and governance with a distributed workforce. The results can be found in our inaugural Data Governance Trends Report. The report offers insights into tools that the 400 IT leaders implemented to help weather the abrupt change, but it also explains the human side of data protection and governance in the age of COVID.
Peace out this holiday season by securing every transaction against card-not-present fraud
We are about to enter the most wonderful time of the year. As consumers increasingly turn towards online and mobile commerce, are you confident in your card-not-present fraud detection capabilities? 2020 has been a year of great surprise and change. While the global health pandemic has changed how we physically interact with each other, it has also revolutionized how we shop.
The Future of Ransomware: Preparing for the Next Generation of Ransomware Attacks
Ransomware has been the scourge of cybersecurity and may have led to a recent death. Now it soon may get way more dangerous The threats to cybersecurity are constantly evolving. As security teams develop solutions to the threats, malicious actors change their tactics to keep chasing their ill gotten gains. After all, the Game is the Game. And the game keeps changing. In recent years, ransomware has been the weapon of choice for hackers looking for a payday.
PCI Logging Rules Your Organization NEEDS to Know
For an organization to be compliant with PCI logging requirements, it must follow PCI Requirement 10 of the Payment Card Industry Data Security Standards (PCI DSS). Below, we’ve listed the highlights of this section and the important details that you need to know.
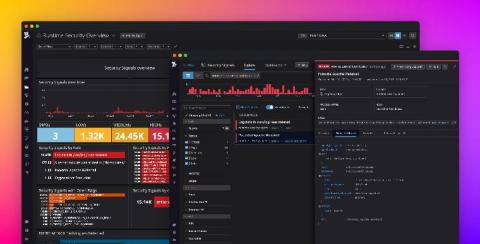
Secure your infrastructure in real time with Datadog Runtime Security
From containerized workloads to microservice architectures, developers are rapidly adopting new technology that allows organizations to scale their products at unprecedented rates. In order to make sense of these complex deployments, many teams are abstracting applications away from the environments in which they run. Because of this trade-off, developers and security teams lose the access to the unified context from infrastructure to application needed to fully secure their services.
Data Protection in the Age of Kubernetes
Software containers are at the heart of cloud-native business transformation initiatives. Containers are a natural evolution from virtual machines to a more granular and portable application environment in clouds. They are designed to support rapid development and deployment of cloud-native applications in what is called a DevOps model, a set of practices that combines software development and IT operations.
Data Protection in the Age of Cloud Native - Part 2
In part 1 of this blog series on Kubernetes and cloud native application data protection, we addressed The need for Data Protection for Containerized Applications. In part 2 of this blog series, we go through.
4 Emerging SaaS Security Risks to Consider in 2021
Last year, we wrote about the threat landscape we saw on the horizon for 2020 in our SaaS threat landscape post. Focusing on apps like Slack, we honed in on the risks that would matter in 2020. Although our analysis was written well ahead of the COVID-19, some of our concerns were exacerbated as a result of the pandemic. With the pandemic continuing into 2021, we wanted to take the time to review the state of cloud adoption in 2020 and update our threat assessment going into the new year.
Anti-Fingerprint Browsers: What You Need to Know
Client-side technology (such as JavaScript) can be used to create a unique “fingerprint” for a specific device/browser combination, which can be used to modify functionality or detect returning users. Some fraud prevention tools will use fingerprinting to block transactions from browsers that have been previously identified as insecure or involved in fraudulent activity.