Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Cybersecurity Maturity Model Certification (CMMC): Tips for Compliance
Following a string of 83 data breaches in 2019 alone, the United States Department of Defense (DoD) established the Cybersecurity Maturity Model Certification (CMMC). The CMMC framework is a unified national standard for improving cybersecurity. Companies in the defense industrial base (DIB) must implement CMMC requirements in order to win contracts. Read on to find out how you can achieve compliance.
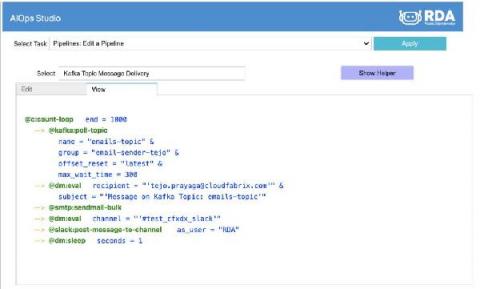
Automatically Sending Kafka Messages to Email or Slack Channel using Software Bots
PHI Compliance: What It Is and How To Achieve It
For organizations that work in or partner with the healthcare industry, HIPAA compliance is of paramount importance. Keeping a patient’s medical records and personal information safe isn’t just a matter of avoiding penalties. It’s also key to building trust with patients and, ultimately, providing great patient care. Here’s what health organizations and their partners need to know about PHI and keeping it secure.
Demystifying Shift-Left Approach in Application Security
Understanding Mobile Application Penetration Testing Methodologies
Mobile Application Penetration Testing Methodology as a security testing measure, analyses security perimeters within a mobile environment. Derived from the traditional concept of application security methodology, its main focus lies on client-side security and it broadly puts the end-user in control. By conducting penetration testing, companies can gain insights into the source code’s vulnerabilities, bottlenecks, and attack vectors beforehand.
Scan for AWS CloudFormation misconfigurations with Snyk IaC
We’re excited to announce the launch support for AWS CloudFormation in Snyk Infrastructure as Code. In our recent Infrastructure as Code Security Insights report, we found that 36% of survey participants were using AWS CloudFormation (CF) as their primary infrastructure as code tool of choice. Using Snyk Infrastructure as Code, you can now scan your CF YAML or JSON templates against our comprehensive set of AWS security rules.
Privacy Laws Comparison: Russia vs. China vs. USA
The data privacy regimes in Russia, China, and the United States are very different from the regimes elsewhere. The financial lure of selling to, or processing data on, EU residents is strong, which has led other countries to adopt the General Data Protection Regulation (GDPR) or something like it. Russia, China, and the United States are large enough for other forces to dominate, including the desire to have their citizens’ data stored locally, as we’ll see.
Introducing New Cloud Security Monitoring & Analytics Apps
Cloud Threats Memo: Illustrating Big Risks in the Shift to Remote Working
The exploitation of traditional remote access technologies is reaching new records. That, in a nutshell, is the main finding of Nuspire’s Threat Landscape Report Q1 2021. The report, sourced from 90 billion traffic logs during Q1 2021, looks at a range of events such as malware activity, botnet activity, exploitation activity, and remote access. The remote access section probably best illustrates the risks posed by the sudden shift to remote working.