Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Splunk SOAR Playbook of the Month: Investigations with Playbooks
What Is Financial Crime Risk Management (FCRM)?
Securing your cloud networks: Strategies for a resilient infrastructure
What exactly is resilience? According to the U.S. National Institute of Standards and Technology, the goal of cyber resilience is to “enable mission or business objectives that depend on cyber resources to be achieved in a contested cyber environment.” In other words, when you’re at odds with cybercriminals and nation-state actors, can you still get your job done? If not, how quickly can you get back up and running?
How to Handle Secrets with Azure Key Vault
This tutorial details how to manage secrets effectively using Azure Key Vault. You'll learn how to create secrets and access them in both virtual machines and Kubernetes clusters.
Enhancing Code Security with Generative AI: Using Veracode Fix to Secure Code Generated by ChatGPT
Artificial Intelligence (AI) and companion coding can help developers write software faster than ever. However, as companies look to adopt AI-powered companion coding, they must be aware of the strengths and limitations of different approaches – especially regarding code security. Watch this 4-minute video to see a developer generate insecure code with ChatGPT, find the flaw with static analysis, and secure it with Veracode Fix to quickly develop a function without writing any code.
AI can crack your passwords. Here's how Keeper can help.
As AI becomes more advanced, it’s important to consider all the ways AI can be used maliciously by cybercriminals, especially when it comes to cracking passwords. While AI password-cracking techniques aren’t new, they’re becoming more sophisticated and posing a serious threat to your sensitive data. Thankfully, password managers like Keeper Security exist and can help you stay safe from AI-password threats.
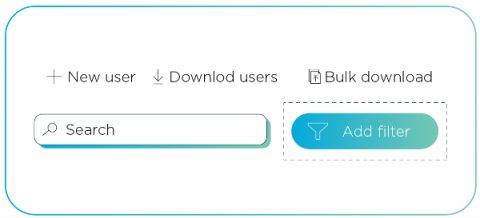
How to revoke access for unwanted guests in Azure Active Directory
Do your house guests still have access to your home after they’ve left, or overstayed their welcome? No, right? You would throw them out or take the keys back because they no longer require access. Guests in Azure are like house guests. Once they no longer need access, it's then time to take back the key so they no longer have access to the company's data and connected apps. Yet many organizations are inadvertently leaving themselves at risk of supply chain attacks.
Why Digital Security is More Important Than Ever: Expert Tips to Stay Safe Online
Why Should SecOps Pay More Attention to Network Data?
Trying to convince SecOps teams they need more data is like trying to convince a drowning person they need more water. SecOps teams are so overwhelmed they can’t even respond to 67% of the alerts they receive. On average, SecOps teams receive 4,484 alerts per day and spend over three hours per day manually triaging the alerts, costing $3.3 billion annually in the US alone.