Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Considering Passwordless? Here's How to Do It
When creating a new password, you know the drill – it must be at least eight characters long, contain special characters and avoid sequential characters or be based on dictionary words. Although these requirements can be a pain in the neck and seriously hamper end user experience, they are not a sign of officious IT security teams.
The IR Retainer Redefined: Boosting Cyber Resilience with MDR + Cyber Risk Retainer
An effective detection and response capability is essential for monitoring key assets, containing threats early and eradicating them. However, due to the current disparate nature of potential attack vectors within an organization, affording the wide range of sensors necessary can be a challenge as well as the worry of the disruption of critical services. Yet, without robust detection and response processes, businesses are left vulnerable.
How to Ensure the Security of Mobile Gadgets
Seamless Collaboration in Life Sciences: A Key to Success
Biotech companies face an era of opportunities and challenges as data volumes explode and technology rapidly evolves. The pressure to enhance collaboration and efficiently manage data is immense. This article explores how innovative biotechs leverage platforms like Egnyte to transform their operations.
HTTP/2 Rapid Reset Attack Vulnerability
Cisco iOS XE Vulnerability: CVE-2023-20198
Cisco has released an advisory, acknowledging active exploitation of a previously unknown vulnerability, which is tracked as CVE-2023-20198, in the web UI feature of Cisco IOS XE Software when exposed to the internet or to untrusted networks. This vulnerability allows a remote, unauthenticated attacker to create an account on an affected system with privilege level 15 access, which is the highest level of access.
Elevating Enterprise API Security with Wallarm for MuleSoft Anypoint Platform
In an age characterized by digital transformation, APIs serve as the backbone of modern applications, enabling diverse systems to communicate and share data seamlessly. This widespread API adoption, however, exposes organizations to a considerable attack surface, inviting the attention of cyber adversaries searching for vulnerabilities to exploit.
What's XDR? Extended Detection & Response, Explained
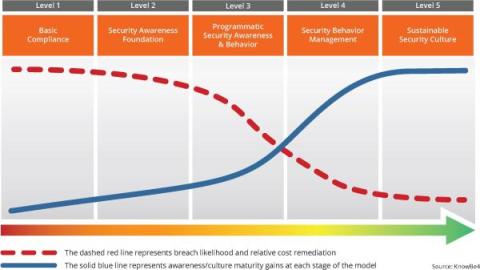
Phishing Tests Start The Virtuous Cycle Of A Strong Security Culture
Phishing tests are the catalyst to achieve a sustainable security culture within your organization. They are actually the start of a virtuous cycle that helps you move up to the highest maturity level. The cycle initiates with Awareness. Phishing tests offer a real-time view into your employees' understanding of phishing threats. They expose your workforce to simulated phishing attempts, making the threat real to them. The immediate feedback from these tests highlights areas for improvement.