Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Mend's Handy Guide to Using EPSS Scores
Is your ID badge giving away too much about you?
The Genesis of "Exodus Logs Market"
21 Ecommerce Fraud Protection Policies to Implement Now
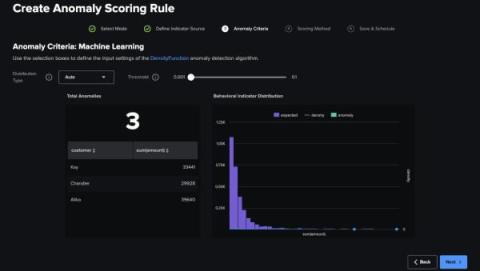
Find the Unusual with the Splunk App for Behavioral Profiling 2.0
Fueling Chaos: Hacker Group Grinds 70% of Iran's Gasoline System to a Halt
Cord cutting: Cables that you didn't know about!
A week before my 15th birthday in September 2023, and quite coincidentally in time for my favorite phone's 15th iteration (cough cough, parents, hint hint), AT&T along with AST-Science successfully made a call. Well, in the 21st century that’s not very “Mr. Watson, come here. I want to see you.”, but this call was on another level, or as one could say, out of this world!
Krampus delivers an end-of-year Struts vulnerability
On December 20, 2023, NIST updated a CVE to reflect a new path traversal vulnerability in struts-core. This is CVE-2023-50164, also listed on the Snyk Vulnerability database, with 9.8 critical severity CVSS. If you’ve been doing cybersecurity long enough, you remember the 2017 Equifax breach, which also took place due to an unpatched Struts vulnerability. In this post, I outline the issue, discuss its severity, walk you through a proof-of-concept exploit, and provide remediation advice.
Using Veracode Fix to Remediate an SQL Injection Flaw
In this first in a series of articles looking at how to remediate common flaws using Veracode Fix – Veracode’s AI security remediation assistant, we will look at finding and fixing one of the most common and persistent flaw types – an SQL injection attack. An SQL injection attack is a malicious exploit where an attacker injects unauthorized SQL code into input fields of a web application, aiming to manipulate the application's database.