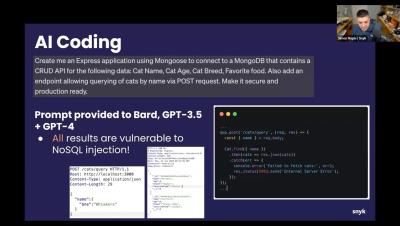
AI Hallucinations and Manipulation: How to Use AI Coding Tools Securely (part 1)
Generative AI can help you write code faster, but is it secure? Learn how you can leverage the power of AI to increase your velocity while mitigating risks and staying secure. Learn from security experts Liran Tal & Simon Maple in a hands-on session where they walk through.