Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Cyber Threats on Sale - A Black Friday Special Intelligence Report
Businesses are Losing Big to Credential Stuffing Attacks
This week it was revealed that a huge credential stuffing attack had cost sports betting organization DraftKings $300,000. More specifically, cyber-crooks had used credential stuffing to gain access to many DraftKings customer accounts via a large-scale account takeover (ATO) attack and withdrawn funds. DraftKings has subsequently reimbursed the affected accounts, leaving the business out of pocket rather than its customers.
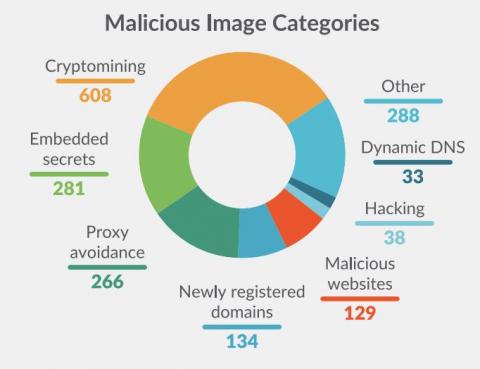
Analysis on Docker Hub malicious images: Attacks through public container images
Supply Chain attacks are not new, but this past year they received much more attention due to high profile vulnerabilities in popular dependencies. Generally, the focus has been on the dependency attack vector. This is when source code of a dependency or product is modified by a malicious actor in order to compromise anyone who uses it in their own software.
General Overview: Cyber Threats in Todays Society
Cyber threats are a big deal in today’s society. It seems like every other day, there is a new scam or cyber attack that is making the rounds. In this blog post, we will take a look at some of the biggest threats and scams that you need to be aware of. We will also discuss how to protect yourself from these attacks.
Killnet Claims Attacks Against Starlink, Whitehouse.gov, and United Kingdom Websites
Pro-Russian threat actor group Killnet claims to have launched DDoS attacks against Starlink and the United States’ government website whitehouse.gov. Starlink is a satellite internet service company operated by SpaceX. In 2019, SpaceX began launching Starlink satellites, and as of September 2022 is reported to have launched more than 3,000 satellites into low-Earth orbit (LEO).
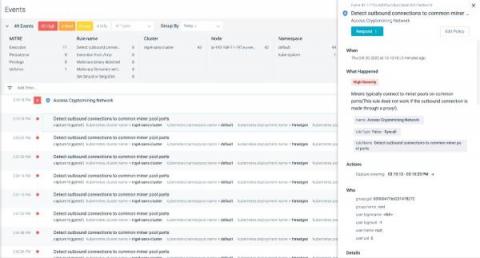
Detecting Cryptomining Attacks "in the Wild"
Cryptomining attacks are becoming more notable in-line with the rise of blockchain and cryptocurrencies, so detecting cryptomining has become a high priority. Security researchers have found data breaches related to various cryptominer binaries running within victims’ infrastructures. The default openness of Kubernetes clusters and the availability of the extensive compute power required for mining makes Kubernetes clusters a perfect target for cryptomining attacks.
Internal Reconnaissance Protection using NetCease and SAMRi10
Internal reconnaissance is one of the first steps an attacker will take once they have compromised a user or computer account in your network. Using various tools or scripts, they enumerate and collect information that will help them identify what assets they should try to compromise next to get what they want. For example, BloodHound will map out attack paths that can enable an adversary to escalate their privileges from ordinary user to admin.
How Did LAUSD Get Hacked in 2022?
Vice Society, the cybercriminal gang responsible for the attack, is believed to have used internal login credentials leaked on the dark web to access LAUSD’s network and launch the ransomware attack. Twenty-three internal LAUSD credentials were leaked on the dark web leading up to the attack, with at least one set granting access to LAUSD’s Virtual Private Network (VPN).
The Top 5 Cyber Threats Facing Businesses Today
Businesses are more vulnerable to cybercrime now than ever before. Hackers are getting smarter and more sophisticated, and they are constantly coming up with new ways to exploit businesses online. If you want to protect your business from cybercrime, you need to be aware of the top 5 cyber threats that are facing businesses today. In this blog post, we will discuss each of these threats in detail and provide tips on how you can protect your business from them.