Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
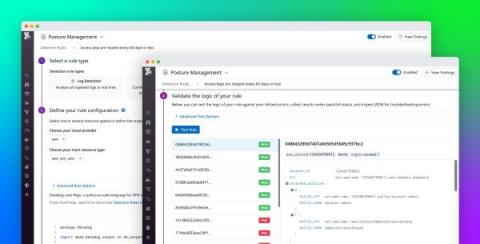
Customize rules for detecting cloud misconfigurations with Datadog Cloud Security Management
For organizations in highly regulated industries, any misconfiguration in their cloud environments can be detrimental to customer trust and privacy if overlooked. To mitigate this risk, DevOps and security engineers follow recognized compliance standards to quickly surface issues in their AWS, Azure, or Google Cloud environments. Organizations can take this work a step further by developing detection rules tailored to their unique business or security goals.
1- Introducing Zaraz
2 - How Zaraz Works
Real-time co-editing on desktop using native Google Workspace tools
With deep integrations into Google Workspace, Egnyte enables users to streamline the document creation process by delivering a seamless experience to create, co-edit and share documents directly from within the Egnyte Desktop App and Web UI. By using Egnyte as the document source, files are also protected from internal misuse and external threats, ensuring that users can collaborate with confidence, without concerns of exposing sensitive data.
Demystifying Elastic Security for Cloud and its capabilities
How SD-WAN and Public Cloud have changed the dynamics when it comes to modern connectivity and infrastructure requirements
Digital and cloud transformation has unlocked new business opportunities and operational efficiencies for organisations. But migration to the cloud also means our approach to deploying applications and services has radically changed, as enterprises move away from traditional data centres. Likewise, flexible working means users have also moved away from traditional offices and branches.
Fix cloud security issues faster and at the source with Snyk Cloud
In July 2022, we announced Snyk Cloud, extending the Snyk developer security platform to secure application and infrastructure configurations in running cloud environments. Today, we’re thrilled to introduce a new feature of Snyk Cloud that enables you to "fix cloud issues in IaC" (infrastructure as code), making Snyk Cloud the first solution to secure the cloud through code with remediation paths in IaC.
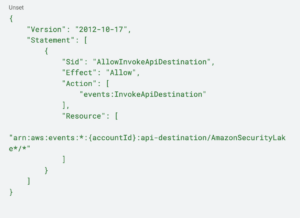
Building Efficient SecOps Pipelines with AWS Security Lake and Torq
What You Need to Know About the Netskope Accelerator Package for Azure
Over its history Netskope has delivered many tools to integrate its various solutions and findings with Microsoft products. We have built multiple integrations with Azure Active Directory, Azure Sentinel, Azure Monitor, and Azure Blob and Compute. All of these are very helpful in unlocking base or advanced functionality to augment Microsoft solutions.