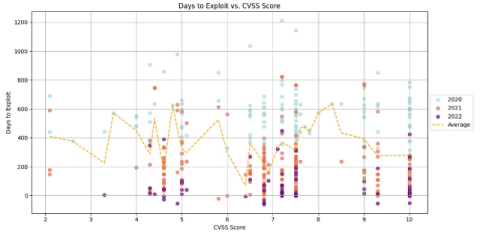
ThreatQuotient Enables Companies to Scale Security Operations Through Effective and Efficient Use of Threat Intelligence
Internal security operations teams work smarter, not harder with cybersecurity automation that balances human workflow management with automation.