Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Corelight
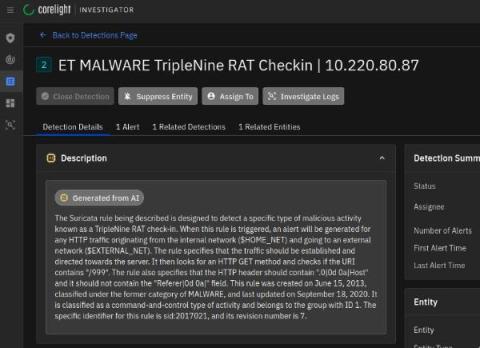
How Corelight Uses AI to Empower SOC Teams
The explosion of interest in artificial intelligence (AI) and specifically large language models (LLMs) has recently taken the world by storm. The duality of the power and risks that this technology holds is especially pertinent to cybersecurity. On one hand the capabilities of LLMs for summarization, synthesis, and creation (or co-creation) of language and content is mind-blowing.
The Art of Team Building: Blueprints from the Black Hat NOC
It has been a distinct honor to be a part of the Corelight team that helped defend this year’s Black Hat events. I started the event season in the Network Operations Center (NOC) at Black Hat Asia, and then capped it off at Black Hat in Las Vegas. In this blog I’ll share my experience and learnings from participating in both NOCs.
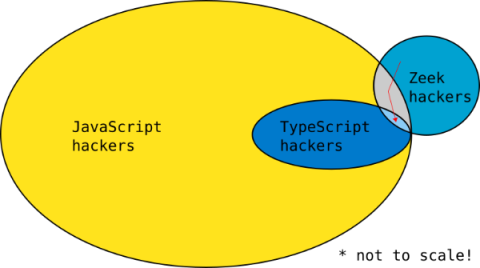
Writing a Zeek package in TypeScript with ZeekJS
Zeek® is the world’s most widely used network security monitoring platform and is the foundation for Corelight network evidence. In this blog I share how to write a Zeek package in TypeScript with a new capability called ZeekJS that was released as part of Zeek 6.0.
Turning the tables on the infiltrator
What happens at the point in time when an organization’s information security is compromised? This blog explores an important paradigm shift that occurs at the very moment of compromise and that can be leveraged to turn the tables on the attackers.
Black Hat NOC USA 2023: Five takeaways for SOC teams
During this year’s Black Hat in Las Vegas, I learned (or was reminded of) many lessons working alongside my Corelight colleagues and Black Hat Network Operations Center (NOC) teammates from Arista, Cisco, Lumen, NetWitness and Palo Alto Networks. The uniqueness of standing up a full security stack and NOC in such a short time with a team that comes together infrequently really forced me to consider how team processes and communication affect NOC/SOC efficiency and effectiveness.
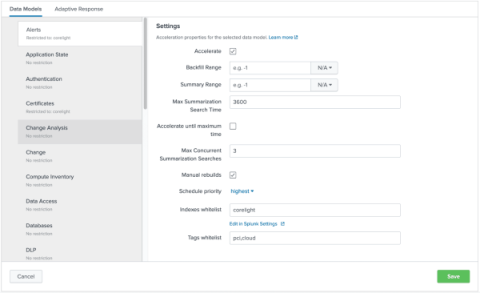
Enhance your search experience within Splunk by using the Corelight App
The Corelight App for Splunk provides the foundation for organizations to boost SOC effectiveness and productivity by using Corelight data in Splunk. In this blog, I’ll walk through how the Corelight App leverages Splunk’s Common Information Model (CIM) to enhance users' search experience when they are using Corelight data.
The Importance of NDR Detection-in-Depth
Using Corelight to Identify Ransomware Blast Radius
Over the past few months, ransomware targeting healthcare organizations has been on the rise. While ransomware is nothing new, targeting healthcare organizations, at the extreme, can impact an organization’s ability to engage in anything from routine office visits to life-or-death diagnoses, treatments, and patient care.