Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Corelight
Corelight Open NDR Now Helps Defend Black Hat Events
We are honored to announce that Corelight’s Open Network Detection and Response (NDR) solution has been chosen by the esteemed Black Hat Network Operations Center (NOC) to help defend their networks at Black Hat events worldwide. It’s a testament to the capabilities of our platform and the open source technologies that power it. We are honored to be among the distinguished vendors chosen to provide best of breed solutions for the NOC.
Threat Hunting Fundamentals: Why Network Data Should Be At Core of Your Process
How Corelight Transforms Data Security with Normalyze
Expand visibility around authentication and application anomalies with Corelight's new LDAP analyzer
Comprehensive visibility into network protocols is a hallmark of Zeek (and therefore Corelight) data. That's why we are very happy to announce that with our v27.2 release we are supporting a new analyzer for the LDAP protocol. You likely know LDAP as a workhorse for carrying directory information across the network. While it's an open standard, it's most often seen as part of several server implementations, especially Microsoft's Active Directory, OpenLDAP, and others.
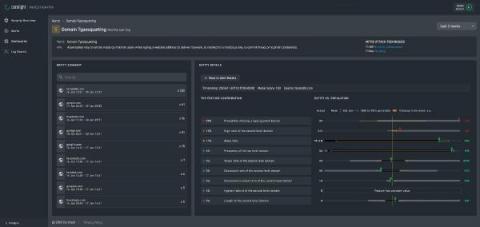
Entity Collection Overview
From Noise to Signal: Enrichment and Routing with Corelight, Cribl, and Elastic
Corelight Investigator introduces new Machine Learning Models
Corelight Investigator furthers its commitment to delivering next-level analytics through the expansion of its machine learning models. Security teams are now enabled with additional supervised and deep learning models, including: We continue to provide complete transparency behind our evidence -- showing the logic behind our machine learning models and detections, allowing analysts to quickly and easily validate the alerts.
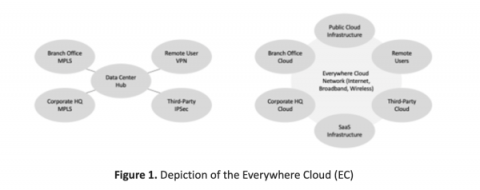
Corelight for the everywhere cloud
Editor's note: This is the first in five-part series authored by Ed Amoroso, founder and CEO of TAG Cyber, which will focuses on how the Corelight platform reduces network security risks to the so-called Everywhere Cloud (EC). Such security protection addresses threats to devices and assets on any type of network, including both perimeter and zero-trust based.