Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Corelight
Corelight Investigator: Ready for Europe
This summer, we launched Investigator, Corelight’s SaaS-based network detection and response (NDR) solution that fuses rich network evidence with machine learning and other security analytics to unlock powerful threat hunting capabilities and accelerate analyst workflows. Today, we are pleased to share that the Investigator platform is engaged in attestation for GDPR to support customer threat hunting and incident response operations across Europe.
Detecting the Manjusaka C2 framework
Security practitioners may know about common command-and-control (C2) frameworks, such as Cobalt Strike and Sliver, but fewer have likely heard of the so-called Chinese sibling framework “Manjusaka” (described by Talos in an excellent writeup). Like other C2 frameworks, we studied the Manjusaka implant/server network communications in our lab environment, and here we document some of the detection methods available. We have also open-sourced the content we describe.
Cloud Insecurities - How to threat hunt in hybrid and multi cloud environments
[Demo Video] Corelight + CrowdStrike Falcon XDR
SANS Protects: The Network
SANS 2022 Report Moving to a State of Zero Trust
How to Benchmark Your Threat Hunting Readiness and Prepare for the Next Step
Network Forensics & Incident Response with Open Source Tools
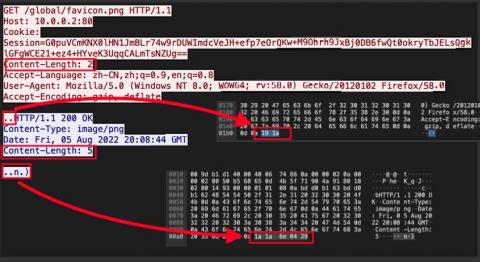
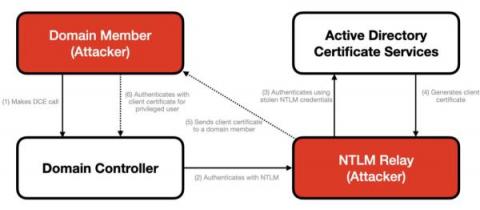
Detecting CVE-2022-30216: Windows Server Service Tampering
In July 2022, Microsoft disclosed a vulnerability in the Windows Server Service that allows an authenticated user to remotely access a local API call on a domain controller, which triggers an NTLM request. This results in a leak of credentials that allows an attacker to authenticate to Active Directory Certification Services (ADCS) and to generate a client certificate that enables remote code execution on a domain controller.